Can IoT Improve Your Quality of Life?
This is the second and last part of Vector Networks attending the IT Connect Conference. If you missed the first article, click here. The article below also includes parts of an interview with René Breyel, co-founder of AIoT Canada.
A few years ago, a company called Smarter released the iKettle – a smart kettle. The iKettle is connected to the Internet via Wi-Fi and can be controlled from an APP installed on your smartphone. You can program your iKettle to start every morning, so you don’t have to do it yourself every day.
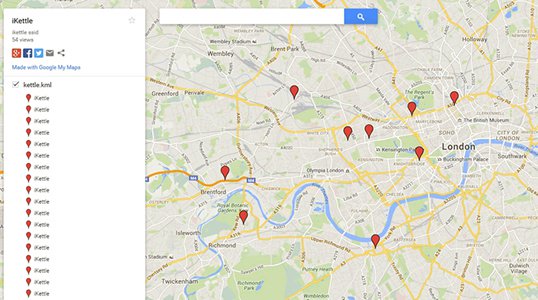
Pen Test Partners took an interest in the device and ran a few tests. More specifically, they tested to see if they could hack into the Wi-Fi networks of those who owned an iKettle. Shockingly, they succeeded. The image below is a map of the locations of the iKettles in London at the time of this study.
What does this mean?
The iKettle did not have proper security measures. And so, the adorable birthday present Sally bought herself became an entry point for hackers to access her Wi-Fi network. Hacking a network can include, but not limited to providing hackers with the ability to do one of the following:
- Changing your Wi-Fi password
- Controlling other devices connected to that Wi-Fi network, like a smart TV or a cellphone
- Finding out the location of your iKettle – most likely where you live
- Using the above to find out other information about you – and potentially stealing your identity
The iKettle is a great example of the vulnerability of an IoT device. If you are unfamiliar with the term IoT, or the “Internet of Things”, it is a concept where any physical object can be connected to the Network to send information and generate valuable insight through the use of smart software, cloud applications or various level of artificial intelligence. This concept applies to more and more devices every day and it is very likely that you have one or more of those devices already in your house like a smartwatch, a connected car, Amazon’s Alexa, a Google Home, a smart TV, an internet-enabled appliance, etc. However, you probably never thought they could pose a threat.
IoT cyber threats for consumers
As we become more reliant on these devices, it may not be surprising that the number of IoT devices is expected to reach over 28 billion by 2022. Unfortunately, as the number of connected devices increase, there will be an increase in cyberattacks as well.
The primary issue is the lack of regulations for securing devices. There are some minimal standards of security that the government of the United States wants to impose. The Canadian government also wants to intervene as they are acknowledging the growth of cybersecurity threats as over half of Canadian households have over four connected devices serving as potential targets.
René Breyel, the co-founder of AIoT Canada, explained that products are evolving too quickly, and businesses aren’t going to slow down this commercial Eldorado to reassure proper security measures. It takes time and resources, that most companies don’t have, to properly secure these IoT devices. But the biggest reason they aren’t spending the time to ensure security is that consumers, or users, are not yet asking for more secure products, mostly because they are not aware of the threats.
Breyel continued to explain that, as consumers, we are not properly managing IoT devices. You would not leave your computer password on a post-it attached to your computer. You would not sell your cellphone without wiping out the data. You would not make a bank transfer while you’re connected to the Wi-Fi at your local café. Therefore, why would you purchase and connect to your home network an IoT device that you aren’t sure is secure?
Consumers view these products as a convenience but are they worth the threat?
IoT for companies
IoT affects companies in multiple ways as well. In one way, IoT attacks are also directed to businesses. The Mirai botnet attack of 2016 attacked over 100,000 poorly secured IoT devices and ended up taking down websites like Twitter, Netflix, Amazon, and CNN.
Another way IoT affects companies is if they should explore the possibility of including IoT as part of their business strategy. Is there a specific industry IoT can benefit? Is there a certain type of product it can benefit? Can it make workflows more efficient? Should it be introduced at all?
René Breyel works with companies to determine whether IoT could improve internal efficiency and add value to their customers. He pointed out that not all markets are ready for smart devices or IoT-related processes. It’s important to manage the risk versus the benefits of the data generated by the object. In other words, what is the risk if we introduce IoT versus what is the downside of not being smart and connected?
Breyel emphasized that IoT, in the end, must generate benefits and clear added value for the company. He developed a very clear step by step process to help companies evaluate and decide if and how to introduce IoT. Before considering technologies, it always includes an assessment of current business processes and understanding of customer objectives. Breyel emphasized the importance of including the customers’ opinion and feedback from the beginning of the process. For more information on how he can help your business, you can contact him directly at rene@aiotcanada.ca
Case Study
The connected mousetrap provides around the clock trap surveillance with real-time trap status. Status of mouse and rat traps include: armed, unarmed or unarmed with a catch. You can place traps thousands of feet away with long-range wireless sensors and receive text and email notifications when there’s activity around the trap. This could prevent costly issues with timely alerts that provide early warnings of infestation problems.
The system is invaluable for collecting data on the efficacy of rodent control strategies, giving a spatial distribution of catches and patterns in rodent activity. Trends can then be linked to events in the food facility that may be inadvertently encouraging the rodent pest population, such as the arrival of a particular delivery, pinpointing the rodent problem and aiding in a solution.
Simple solutions like that could transform the business model of Pest control companies, migrating from a role of technician schedule operator to an advanced data analytics service provider, able to advise and prevent the problem at the source.
Conclusion
I am happy to announce that the new version 3 of the iKettle is now safe to use, that governments are getting involved in cybersecurity and that there is potential for IoT to help companies make money. What are your thoughts on IoT? Cybersecurity?