Back to Basics: What is Shadow IT?
Shadow IT is getting more attention with the steady rise of cloud services within organizations. You might be wondering what exactly shadow IT is, and how to best prevent it. For this Back to Basics post, we will cover the general concept of shadow IT, but stay tuned for an upcoming post that goes deeper into tactics for avoiding this problem.
The term shadow IT refers to employees signing up for online cloud services on their own, without authorization from IT. Here is a quick example to illustrate why this may happen. Let’s say Employee A is working on a project, and he or she encounters a problem preventing them from completing the task at hand. Now, picture the organization’s typical IT department – there is a potentially large pile of requests scattered around desks, which will likely take time to go through. Employee A anticipates a delay so they just do a quick Google search and find a cloud service which resolves the issue. They immediately signup and get on with their project, expecting to figure out any additional paperwork later. Sounds fine, right?
Wrong! By signing up for cloud solutions without the necessary IT approvals and checks, employees are running the risk of putting their organization in compliance troubles with potentially sensitive organization or customer data been stored on unknown servers. On top of this, money is likely being wasted because the employee signing up is unaware of the existing subscriptions across the organization that may be causing doubles or similarities that could be avoided.
In the case of shadow IT, the time-saving benefits are far less critical than the risks that come with unauthorized cloud subscriptions. One of the most difficult aspects of shadow IT is that it’s extremely hard to track, so once employees start foregoing the proper approvals, things can get out of hand quickly. In fact, only about 8% of organizations can track shadow IT as of now, and that number is dangerously low.
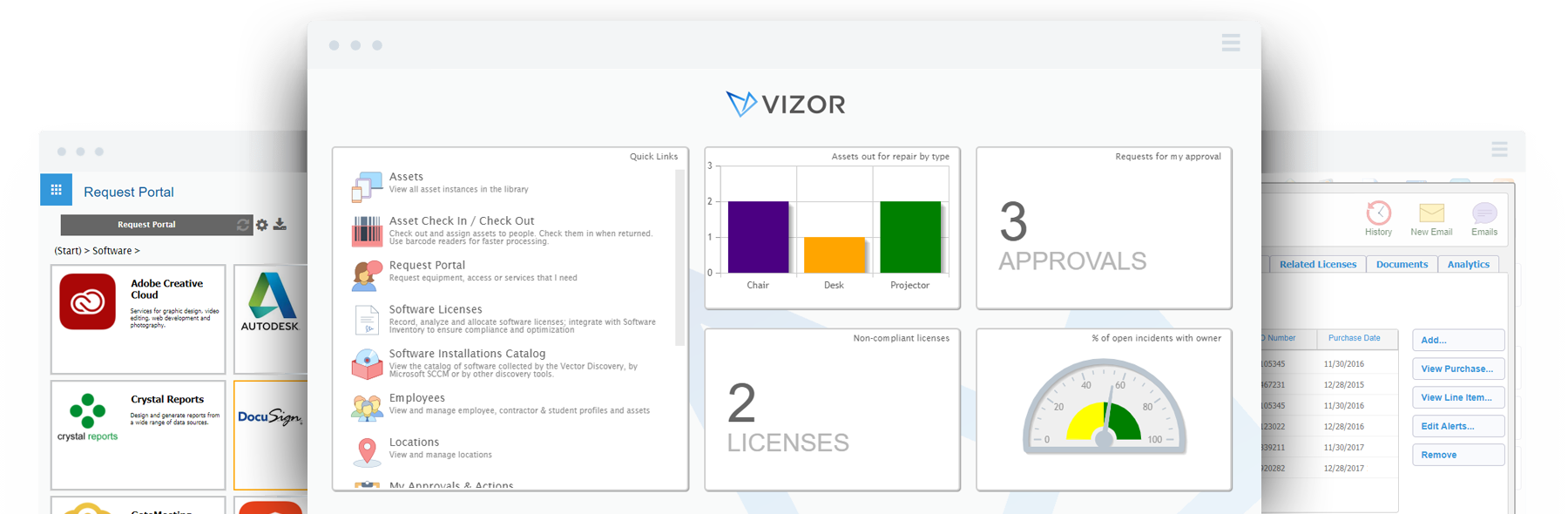
Struggling to manage Cloud Apps?