Pirated software: are you sure you are in the clear?
Software Asset Management: fundamentals for compliance
Many organizations are grappling with the twin problems of adequately identifying the software they have installed, and correctly interpreting the usage entitlements defined in the pages and pages of software licenses they hold. New laptops and netbooks will often come pre-loaded with suites of utilities – some of them from suppliers you have never even heard of. You are probably now the licensee for all these applications as well.
Completing a full compliance snapshot analysis, and then maintaining it, is challenging and time consuming. But, for all your good efforts on these aspects of compliance, you are still at the mercy of the genuineness of the license documents you hold. Audits today may well involve your being asked to provide proof that the grant of entitlement runs all the way back to the software publisher. So, if you bought a system with software pre-installed, you may need to ask the system builder to document the entitlement under which they installed that software. Your responsibilities in compliance extend to ensuring the licenses you have are valid, as well as enough in quantity.
The piracy threat to good Software Asset Management practice
The recent study conducted by IDC on behalf of the BSA concluded that 2009 saw around $1bn of pirated software installed in the UK alone. Much of this has been sold over the internet, and although a substantial portion goes to home users, many smaller organizations will be tempted by the low prices on offer for what looks like perfectly valid copies of leading applications. In a statement in 2008, the BSA stated they had in that year alone forced termination of over 18,000 auctions of software on the internet. Another temptation to which employees can succumb is to purchase a low price academic use license, with discounts of 80% offered on Adobe software for example, nominally for a member of the family, but with the software ending up installed on the employee’s corporate laptop. This is likely to be deemed to be piracy.
With the increasing percentage of corporate systems that accompany their users at home or on the road, the ability to keep inventory monitored through the internet is a must-have.
Avoiding software piracy – the obvious choices
Care and caution over software sourcing becomes paramount. As the BSA – and others – point out, if a price appears to be too good to be true, then it probably is. Systems bought from the major hardware vendors can reasonably be expected to include licenses for the software that is pre-installed, but that cannot be taken for granted when it comes to refurbished systems; a system being offered for less than the normal price of the software installed on it must be viewed with some scepticism. You can also assume nothing with regard to the systems you have inherited through taking over another organization. If you are being asked to absorb another organization’s IT, you should demand that a full compliance analysis comes with the systems you inherit. Whether you will get one is another matter entirely…
Strict regulation of user-installed packages is vital, but this is really only possible with change detection of software inventory, correlated against newly authorized installations via Change Management.
Software license compliance is one of those challenges that’s a little like herding cats, with the ways in which another escape occurs just when you think you have it all secured.
It’s also an objective that has to be communicated with and shared with your users, so they can play their part. In fact, that’s a great place to start.
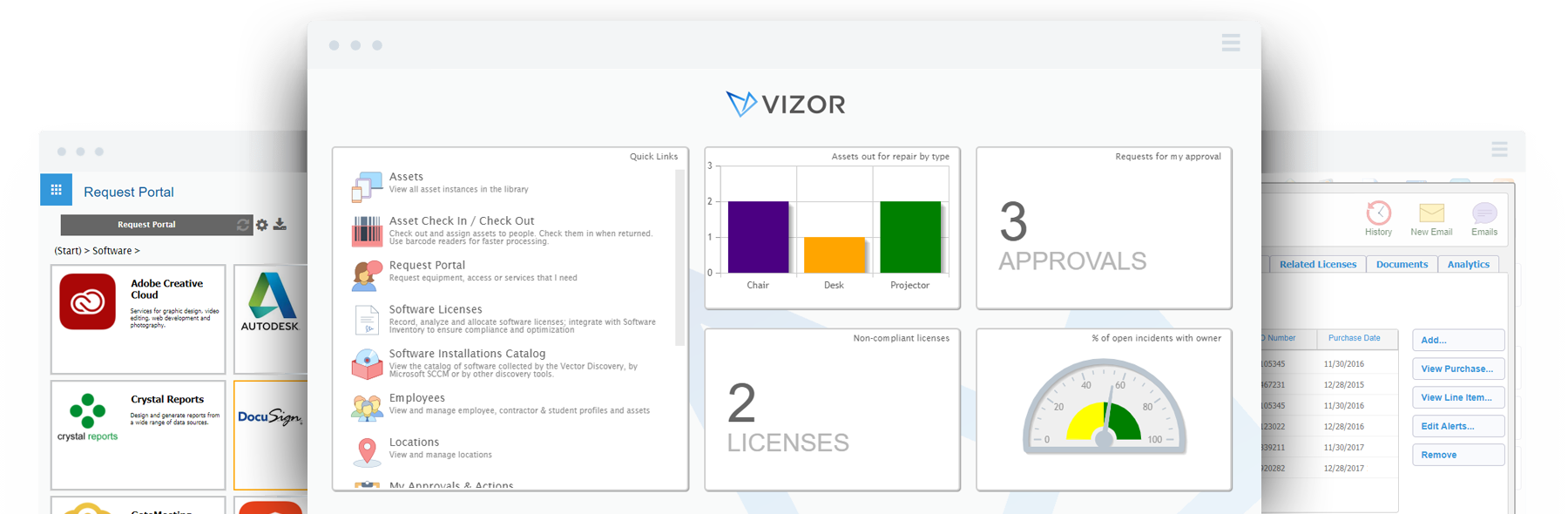
Do you need a tool to manage Software Licenses?